
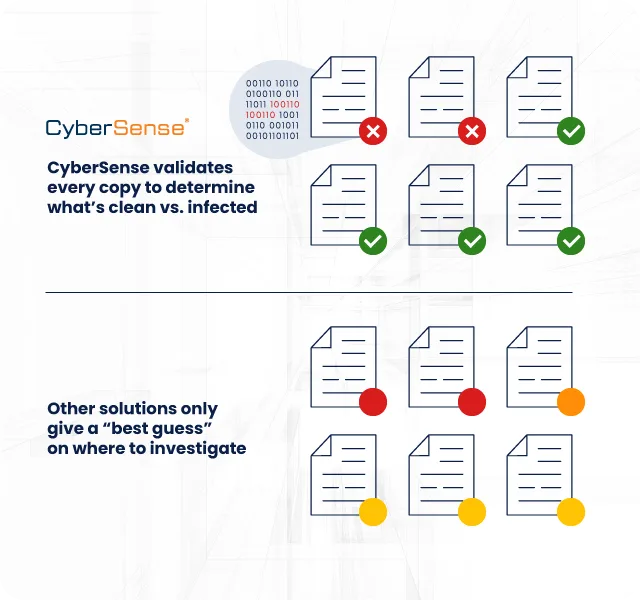
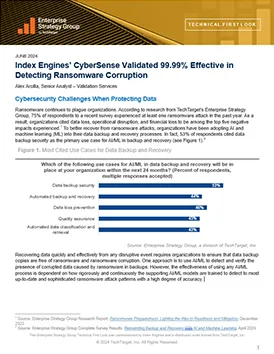
CyberSense delivers what others can’t— trusted data integrity for confident ransomware recovery. By using AI trained on real ransomware to detect data corruption with 99.99% accuracy, CyberSense enables organizations to identify clean recovery points, restore safely, avoid reinfection, and minimize the impact of cyberattacks.

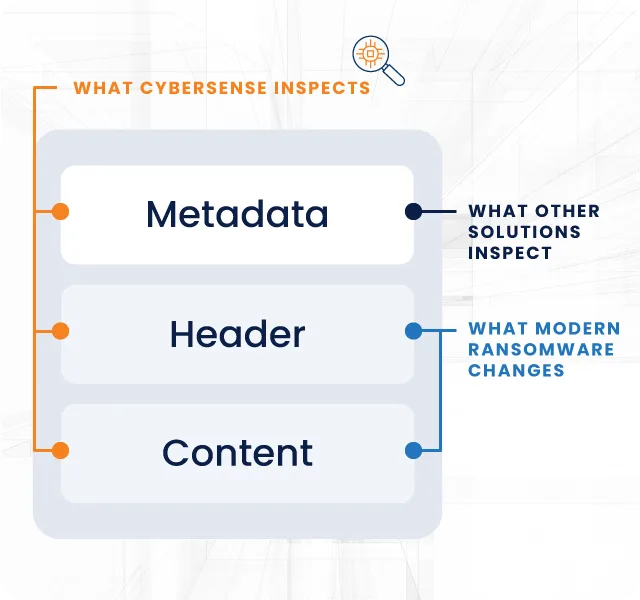
Modern ransomware hides in environments for weeks, using advanced techniques like partial encryption and subtle corruption that evade traditional metadata and signature-based detection.
While antivirus tools focus on prevention and backup solutions only confirm existence, neither validates data integrity at the byte level—meaning immutable backups can still contain infected data.
Learn How
Variant |
Description |
Common |
CyberSense |
|---|---|---|---|
| AlphaLocker | Maintains original metadata | Metadata will FAIL | Analysis of content will detect corruption |
| WhiteRose | Slow corruption <1 file/sec. to evade thresholds | Thresholds will FAIL | Malicious changes in small number of files will detect corruption |
| Xorist | XOR encryption with no changes to entropy or compression | Detection of encryption using compression rates will FAIL | |
| Chaos | Base64 encoding to minimize entropy or compression | 200+ analytics with analysis of content will detect corruption | |
| LockFile, BianLian | Partial/Intermittent encryption |
CyberSense accelerates recovery by generating forensic reports with every scan and pre-identifying the clean recovery point—before an attack occurs. It enables near-instant MD5 searches across existing backups without re-scanning, dramatically reducing investigation time and restoration workflows, saving your business time and money.
– CyberSense generates forensic reports with every scan—not only after an attack
– Every scan also pre-identifies the current clean recovery point
– Run near instantaneous searches of MD5 signatures across existing backups—no need to re-scan
– Significantly accelerates investigation and restoration workflows, bringing the business significant savings
– No preemptive forensic reports; run/build reporting during crisis, while systems may be offline
– Theat hunting that requires writing rulesets and re-scanning backups during crisis
– No pre-identified clean recovery points forces organizations into a trial-and-error restore selection
– Slower investigation and restoration workflows cripple operations and bottom line of business
 ↑
↑